Coveware by Veeam experts have observed a sharp rise in Akira ransomware cases, with more than 40 of those incidents tied to a single exploitation pathway. At the center of these cases is a recently mitigated VPN vulnerability in widely deployed enterprise appliances, which Akira has been actively exploiting to gain initial access. What makes this surge particularly concerning is that many of the victim organizations had already applied the vendor’s patch. On paper, their systems were protected; in practice, attackers were still able to move in.
At a technical level, the flaw involved improper access controls in certain SSL VPN implementations. A patch has been available for some time, meaning this was not a zero-day exploit. Yet exploitation has persisted. Why? Because patching closed the immediate vulnerability, but it did not remove the residual risks attackers could still exploit. Among the most common:
- Persisting local accounts that carried forward during infrastructure upgrades.
- Credential reuse from past breaches or info-stealer malware.
- MFA gaps, where local or emergency accounts were excluded from strong authentication.
While alarming, this is not surprising. Current social engineering ransomware trends show Akira and other groups have learned to capitalize on intersections such as these — where technical flaws get them through the door, and weak credential hygiene keeps it propped open.
Why Patching Wasn’t Enough
Even fully patched systems fell victim due to a convergence of operational oversights that extended far beyond the VPN software flaw itself. Many organizations carried over local administrator and user accounts that had been created years earlier and were no longer actively monitored. These legacy accounts became low-visibility weak points, providing attackers with footholds that defenders often overlooked.
Compounding the problem, threat actors had already amassed valid usernames and passwords tied to these accounts — whether harvested during prior breaches, siphoned off by info-stealer malware, or obtained from dark web marketplaces. In many cases, the attackers were simply waiting for the right opportunity to use them.
While MFA was widely deployed for standard user access, these local and fallback accounts frequently slipped through the cracks. Exempted from MFA requirements and often secured with weak or reused passwords, they created an unguarded entry path. The vendor’s patch closed the underlying flaw, but for adversaries the fix was irrelevant. With valid credentials already in hand, Akira operators no longer needed the exploit at all. They could log in directly through the VPN as if they were legitimate users, bypassing the patch, maintaining access, and moving quickly to deploy ransomware.
The result was a bypass of the vendor fix, persistent access into targeted environments, and the ability to rapidly escalate toward ransomware deployment.
Credential Hygiene Matters
The critical lesson is clear: credential hygiene is as fundamental as patch hygiene. A system may be fully up to date, yet still exposed if attackers can leverage weak or overlooked credentials. Patching closes the software vulnerability, but if legacy access pathways remain open, adversaries will simply walk through them.
To meaningfully reduce this risk, organizations should start by resetting and rotating all local accounts during or immediately after infrastructure upgrades. This ensures that outdated credentials — often carried forward silently over multiple generations of infrastructure — cannot later be weaponized.
Equally vital is the universal enforcement of MFA. No exceptions should exist for “emergency,” fallback, or service accounts. These exceptions, while convenient, are precisely the weak seams that attackers probe; with weak or reused passwords, they effectively provide adversaries with privileged access on demand.
Defenders must also routinely audit and retire dormant or legacy accounts that no longer serve a business purpose. Such accounts often persist in the shadows of identity systems, invisible until exploited.
Resilience comes not from one control but from their intersection. By aligning these identity and access reviews with established vulnerability management processes, security leaders can ensure that patch hygiene and credential hygiene advance in lockstep. Patches may secure the code, but only disciplined credential practices close the door on adversaries. When both are applied consistently, organizations dramatically shrink the attack surface and blunt campaigns like Akira’s before they can gain traction.
The Bigger Picture
This wave of incidents reflects Akira’s sustained presence in the ransomware ecosystem. Akira has been Coveware by Veeam’s #1 tracked threat actor for eight consecutive quarters, and with this latest surge, the group is on pace to extend that streak into Q3 2025. Their persistence demonstrates both the maturity of their operation and the adaptability of their affiliates, who consistently exploit whichever initial access methods prove most effective in the moment.
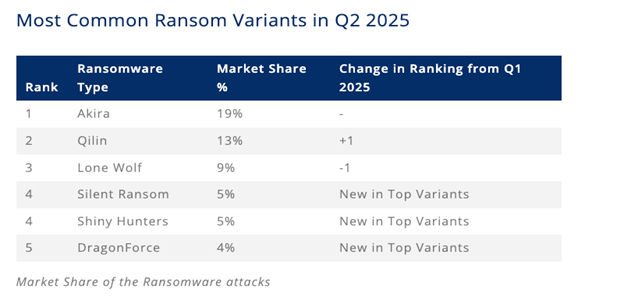
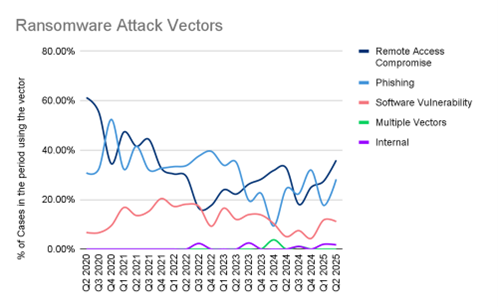
Coveware by Veeam has already responded to dozens of cases linked to this specific exploitation campaign, underscoring a broader industry trend: remote access compromise, often driven by credential-based intrusions, and software vulnerability exploitation remain the two of the three most common on-ramps for ransomware.
But Akira is only one piece of the picture, and other groups have shown that you don’t always need a software flaw to break in. Scattered Spider, for example, weaponizes social engineering against help desks, impersonating employees with such persistence that companies often end up shutting down their own operations just to contain the breach. Shiny Hunters go further upstream, exploiting outsourced personnel and business process outsourcing (BPO) partners to gain access to SaaS environments like Salesforce. Either way, whether through vulnerabilities or social engineering, attackers converge on the same weak point — identity and trust.
Recovery from ransomware requires building resilience long before an incident unfolds, and true resilience means layering defenses so that if one control fails, others are there to catch the threat.
The key takeaways here are as follows:
- A patched system is not automatically a secure system. Attackers look for the weakest link, and patching alone doesn’t address all points of entry or mitigate the openings left behind by vulnerability.
- Patching must be paired with strong credential and identity management practices. Without this, vulnerabilities in authentication resurface in new forms.
- Attackers exploit human and operational gaps in equal measure as technical flaws. Security must extend beyond code to encompass processes and people.
Credential hygiene is at least as important as routine patching, and it should be treated as such. That means reviewing firewall and VPN accounts, rotating credentials regularly, enforcing MFA without exceptions, and disabling dormant or legacy access points. These practices ensure attackers cannot exploit the very gaps left behind after a patch is applied.
Patching a vulnerability is necessary, but it is not always sufficient. If identity controls are weak, attackers will exploit them just as readily as unpatched code. Resilience comes from giving credential hygiene and access governance the same priority as patch management, ensuring that defenses work together rather than in isolation. This means aligning people, processes, and systems so that readiness is embedded into both culture and infrastructure. In doing so, organizations can respond with clarity, adapt under pressure, and emerge stronger from every incident.
The post Akira Exploits the Gaps Between Patching and Identity Security appeared first on Veeam Software Official Blog.
from Veeam Software Official Blog https://ift.tt/27P5Dik
Share this content: